- 08 Nov 2023
- 2 Minutes to read
- Print
- DarkLight
- PDF
Ransomware - Immutable Backups Guide for Microsoft Azure
- Updated on 08 Nov 2023
- 2 Minutes to read
- Print
- DarkLight
- PDF
Ransomware

Microsoft Azure Blob Storage provides a low-cost, scalable cloud storage location for secure off-site data protection. Immutable Storage for Azure Blob enables customers to lock files that are under a certain age in that bucket. PDF version also available.
Overview
Ransomware attacks are increasingly sophisticated, having the capability of watching for cloud account credentials, deleting backups and cloud storage, then encrypting everything and demanding a ransom. It’s imperative to build defenses against this escalating attack. SMBs and large businesses need a backup target that allows them to lock backups for a designated time period. Many of the major cloud providers now support object locking, also referred to as Write-Once-Read-Many (WORM) storage or immutable storage. Users can mark objects as locked for a designated period of time, preventing them from being deleted or altered by any user.
Retrospect Backup integrates seamlessly with this new object lock feature. Users can set a retention period for backups stored on supporting cloud platforms. Within this immutable retention period, backups cannot be deleted by any user, even if ransomware or a malicious actor acquires the root credentials. Retrospect Backup’s powerful policy-based scheduling allows it to predict when those backups will leave the retention policy and protect any files that will no longer be retained, ensuring businesses always have point-in-time backups to restore within the immutable retention policy window.
Using ProactiveAI for advanced scheduling logic, Retrospect provides a rolling window of immutable backups, combining forever-incremental backups with point-in-time restores even after the initial backup passes out of the immutable retention policy.
For more information about backing up to Microsoft Azure Blob Storage container with Retrospect Backup, see
Step-by-Step Guide
Retrospect Backup makes it easy to back up to Microsoft Azure Blob Storage container. Let’s walk through the steps for creating a bucket with a Bucket Lock retention policy.
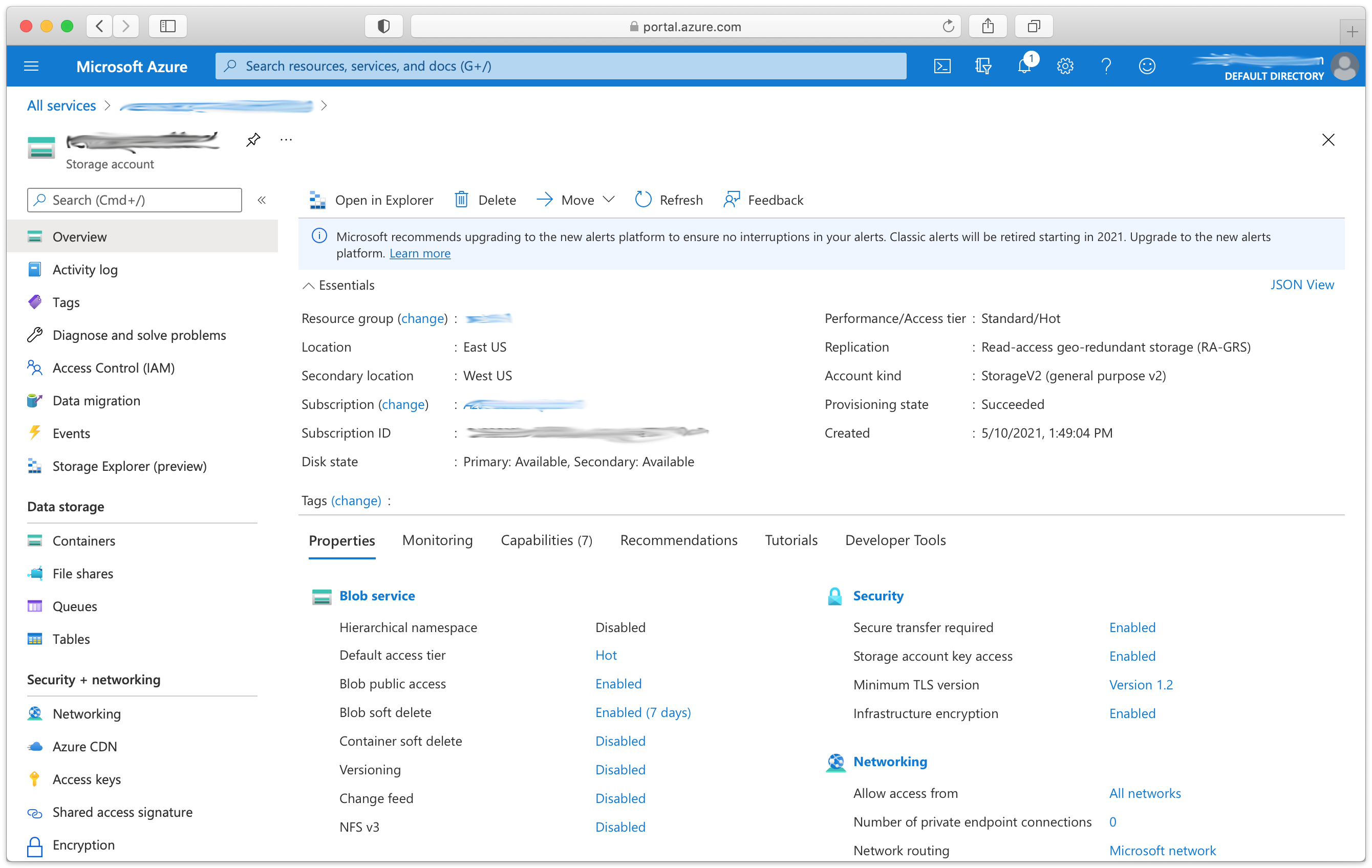
Microsoft Azure: Create a Microsoft Azure Blob Storage Account if you have not already.
Microsoft Azure: Click "Containers".
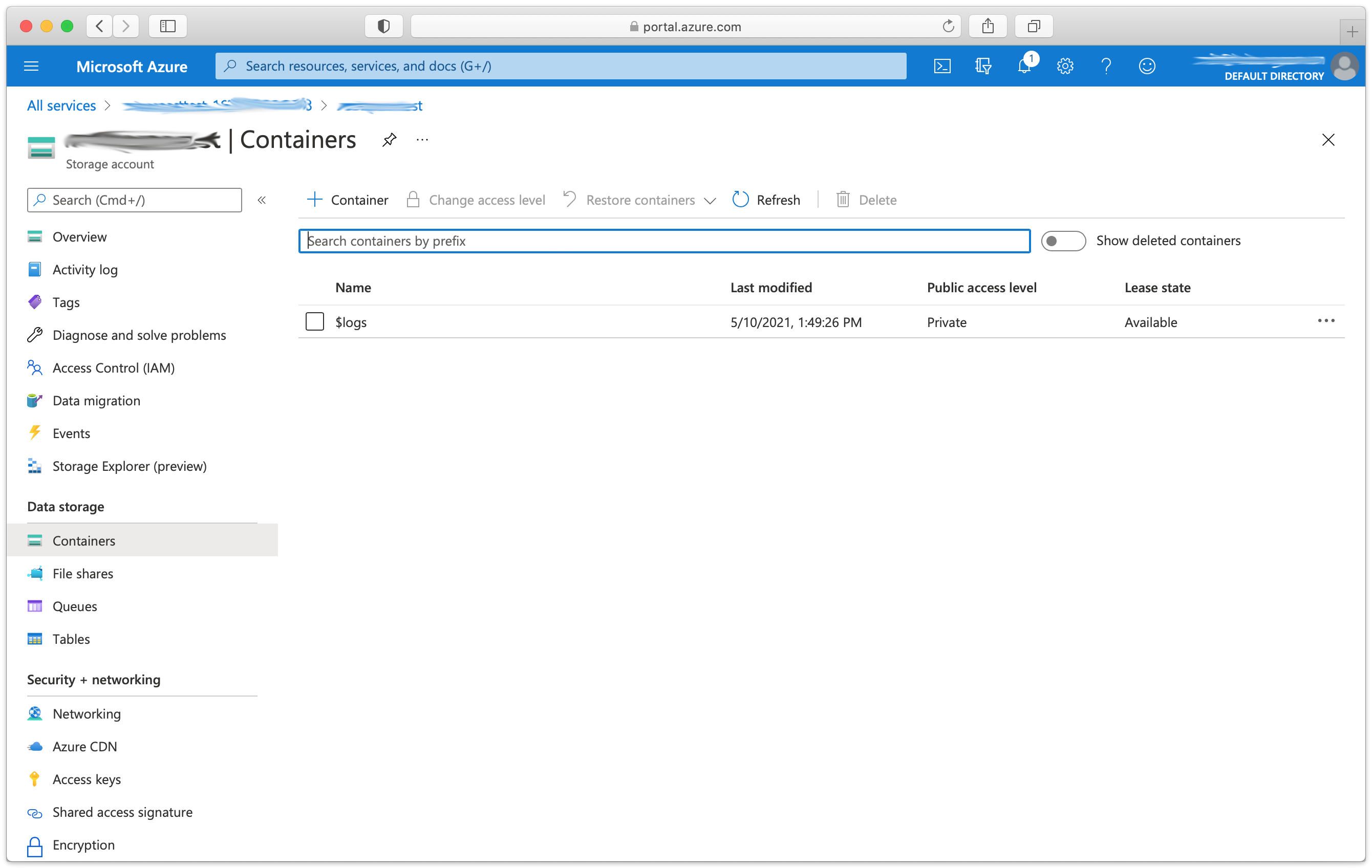
Microsoft Azure: Click "+ Container". Fill out the name and click "Create".
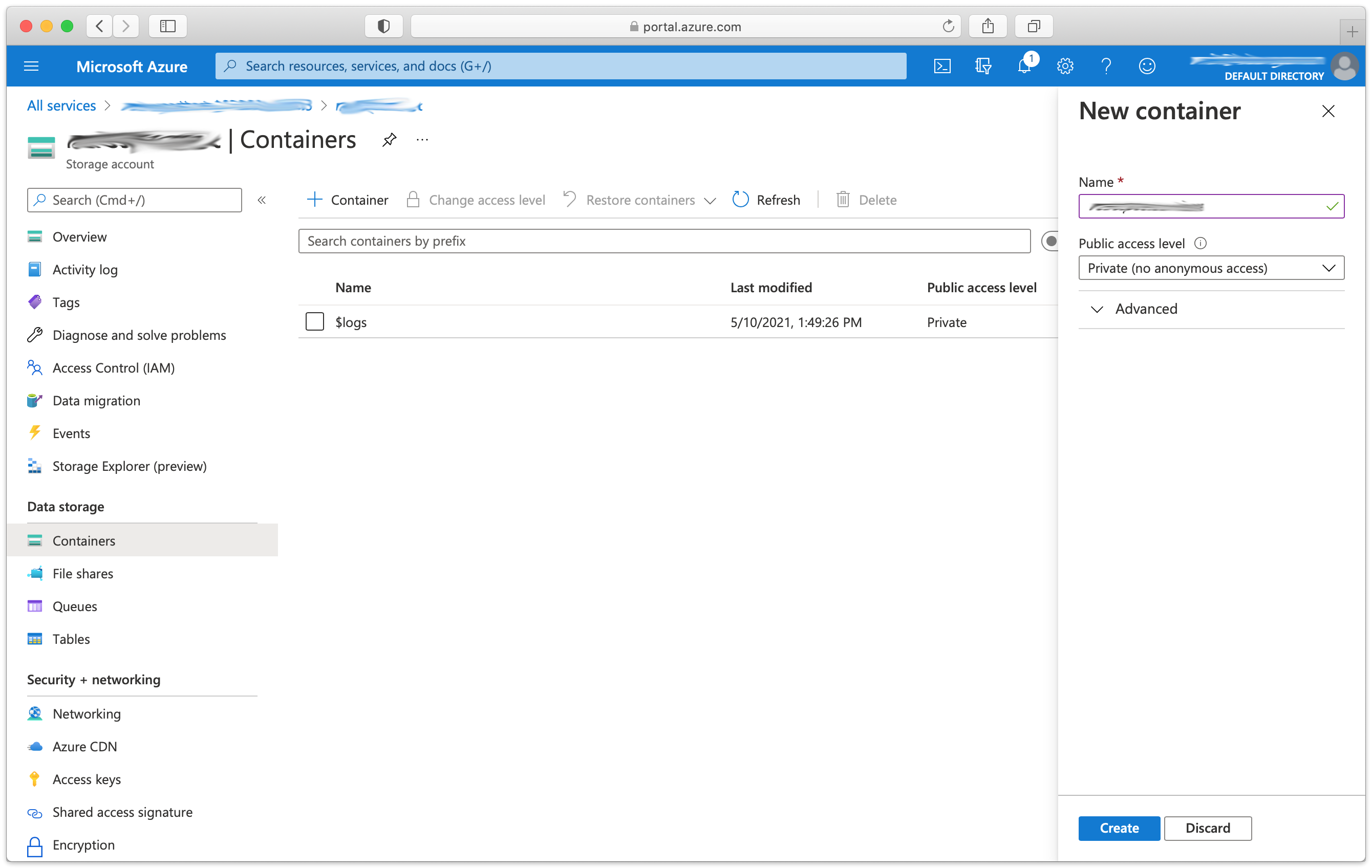
Note that you can also add an immutable storage policy to an existing blob container.
Retrospect: Add a destination. On Windows, select "Backup Sets" then "Create". On Mac, select "Media Sets" and click "Add". Select type "Cloud". Select the appropriate "Immutable Retention Policy" with the number of days you’d like to lock your backups. Add the path and credentials.
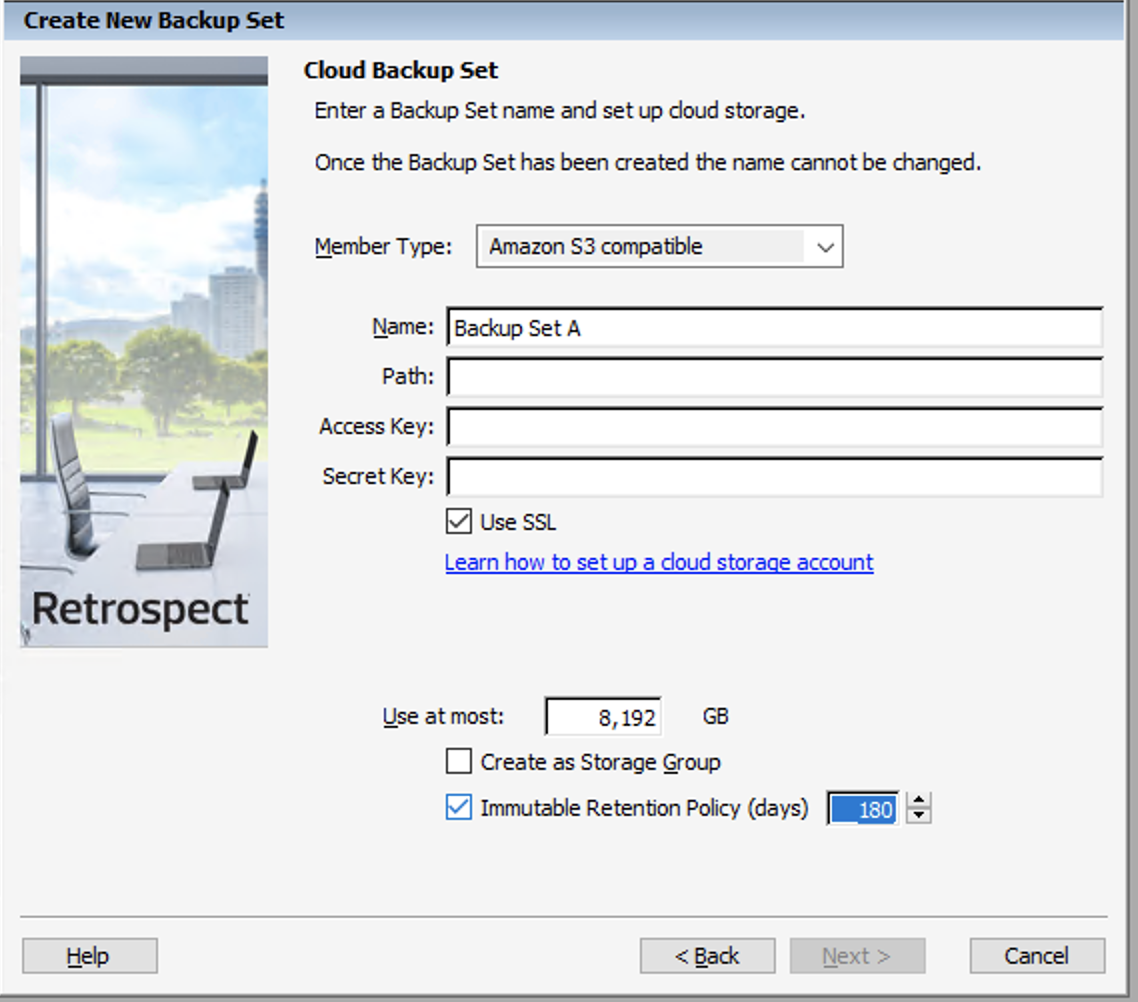
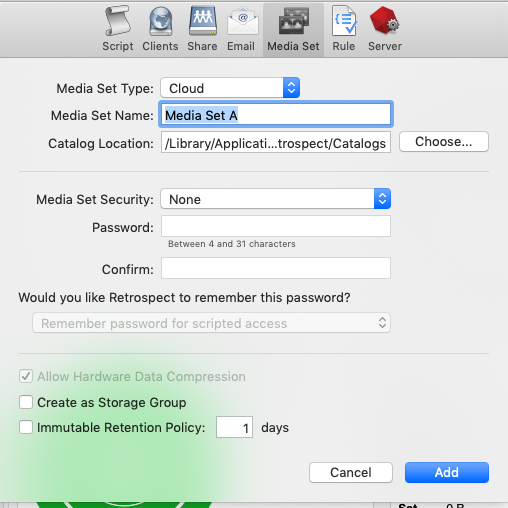
Retrospect: Add the destination to a script and start protecting your data in Microsoft Azure Blob Storage.
Under The Hood
Every backup within the retention period is an immutable backup with point-in-time restore capabilities. Because each backup is incremental, Retrospect only transfers the files that are new or have changed since the last backup. However, you can always restore any part of a backup in Retrospect.
Retrospect Backup uses its advanced scheduling workflow to make sure every immutable backup includes all applicable files. Let’s say the chosen retention period is 90 days, and backups occur every week. Retrospect Backup starts backing up. When it gets to Day 85, it looks ahead to the upcoming back on Day 92, marks which files will no longer be protected on that date based on when they were last backed up, and adds them to the new immutable backup.
With the grooming policy set to match the retention policy, Retrospect will automatically delete the backups that are no longer immutable, saving you storage space while ensuring every file is protected by an immutable backup.
The maximum allowed retention period by Retrospect is 9,999 days.
Versions
Retrospect Backup added support for per-version blobs in Retrospect Backup 18.5. Please upgrade if you are using Retrospect 18.0 to 18.2.
Last Update: February 15, 2022