- 22 Jan 2024
- 3 Minutes to read
- Print
- DarkLight
- PDF
Retrospect for Macintosh Encryption and Security
- Updated on 22 Jan 2024
- 3 Minutes to read
- Print
- DarkLight
- PDF
The following screen appears when securing a new Media Set:
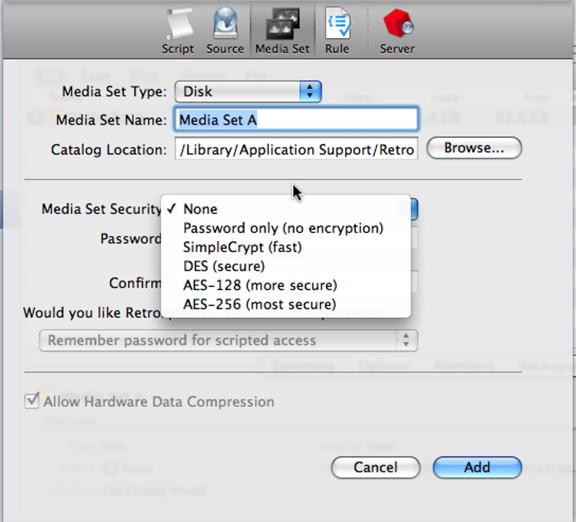
- Password Only (no encryption) – The data itself is unchanged, but a password is required whenever the media set is accessed.
- SimpleCrypt (fast) – SimpleCrypt uses a proprietary Vernam cipher with cipher-block chaining and was designed to be both fast and secure. It provides commercial-level security without appreciably slowing the backup process on all but the slowest computers. SimpleCrypt is more than adequate for the vast majority of users' requirements.
- DES (more secure) – DES (Data Encryption Standard) is an advanced form of data encryption that achieves bank-level security. The effect on backup speed is entirely dependent on the processor, but may take three to four times as long as an equivalent backup to a media set that is not encrypted. Only the most security-conscious organizations require this level of data encryption.
- AES-128 or AES-256 (most secure) – AES-128 and 256: provides password protection and encrypts Media Set data using the Advanced Encryption Standard. AES-128 and 256 provides the best combination of security and performance. This is US Government certified.
- Saving the Media Set Password – Retrospect can store the Media Set password for you so you do not always have to enter it to use the Media Set. Go to Media Sets, select the desired Media Set, click Options.
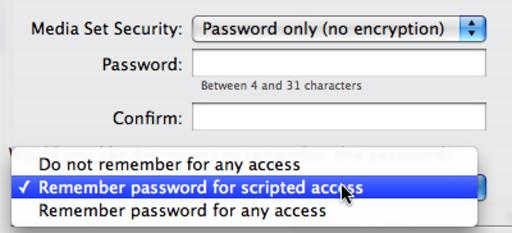
If the Password options are dimmed, the Media Set was not secured when it was created. You can’t add security to an unsecured Media Set.
- Ask for any access – Retrospect will prompt the user to enter the Media Set’s password, preventing unattended operation. This is the preferable setting if many people have access to the backup computer.
- Save for scripted access (default) – The password is not required for scheduled executions of scripts, but Retrospect still requires that the user enter the password for all other uses of the Media Set. This includes Media Set configuration and any action involving a Browser of that Media Set, such as immediate backup and immediate restore.
- Save for any access – You will never be asked for the password unless the configuration file is moved, deleted, or lost.
IMPORTANT: You must remember the password for your encrypted media sets. Retrospect does not offer a password recovery or password reset option for media set encryption. It is impossible to recover a lost media set password.
Client Security Code
You, as the backup administrator, assign client security codes when installing new clients. You can add or change a security code from the client configuration window under Sources. Select the client source and click the password button on the toolbar.
The codes are stored both in the configuration file and in the client software itself. If the configuration file is removed, you must provide the client security code before each client can be logged in again.
It is important for backup administrators to keep records of all passwords, including security codes. If the configuration file is removed and the security codes are lost, the administrator must re-install all clients with the original software.
Retrospect 8.x and later also supports public and private keys so that clients can all be configured to use the same public key. See Retrospect documentation for more detail.
Network (Link) Encryption
This option ensures that someone cannot access data sent across the network with a network-monitoring tool. This uses network encryption and slows performance by about 10%.
To enable link encryption the client must be logged in.
To enable link encryption for a logged-in client, go to sources. Select the client and click on Options. Retrospect takes you to its client properties window. Click the Encrypt Network Link checkbox.
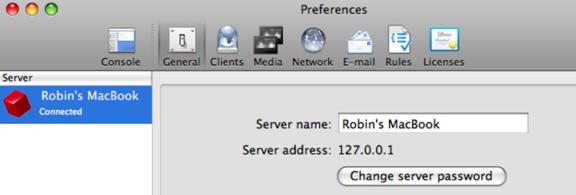
Password Protect access to Server
You can password protect the Retrospect 8 and later server (the engine) so that other copies of the Retrospect Console cannot connect to the engine. Go to Preferences>General and click Change Server Password. Retrospect 19 added multi-factor authentication for the engine.
Additional Security
If you desire a higher level of security, you should rely on other measures such as physical network/media/machine security and local encryption of the data on the original hard drive.
Security Notification
If you suspect that Retrospect security features have been compromised due to a product defect, please email [email protected].
Last Update: January 2025